24,000 Fake Accounts- The Real Warning Sign in the AI Arms Race
The most alarming detail in Anthropic’s recent disclosure is not the 16 million queries. It is the 24,000 fraudulent accounts.
That number changes the story.
According to Anthropic, industrial-scale extraction campaigns targeted its Claude model using roughly 24,000 fake accounts, allegedly linked to three Chinese AI companies. These accounts were used to systematically probe Claude’s reasoning, coding, tool use, and agentic behavior in order to accelerate the training of competing models.
This was not random misuse. It was structured, coordinated, and engineered at scale.
Distillation itself is not controversial. It is a legitimate technique when a company trains smaller versions of its own models. But when 24,000 fraudulent identities are created to interrogate a competitor’s frontier system, this moves beyond competitive pressure. It becomes industrial capability extraction.
The key issue is not only that Claude was queried millions of times. The issue is that existing verification and identity controls allowed tens of thousands of fraudulent access points to operate simultaneously.
That reveals something deeper: AI infrastructure is now a strategic target, and identity systems are the frontline.
Anthropic described how proxy networks using “hydra cluster” architectures distributed traffic across thousands of accounts to evade detection. When one account was banned, another replaced it. In one case, a single proxy network allegedly managed more than 20,000 fraudulent accounts at once.
This is not amateur scraping. It is organized infrastructure.
The implication is stark. If 24,000 fraudulent accounts can operate long enough to generate 16 million structured extraction queries, the vulnerability is systemic. It is not just about one company’s model. It is about the scalability of abuse.
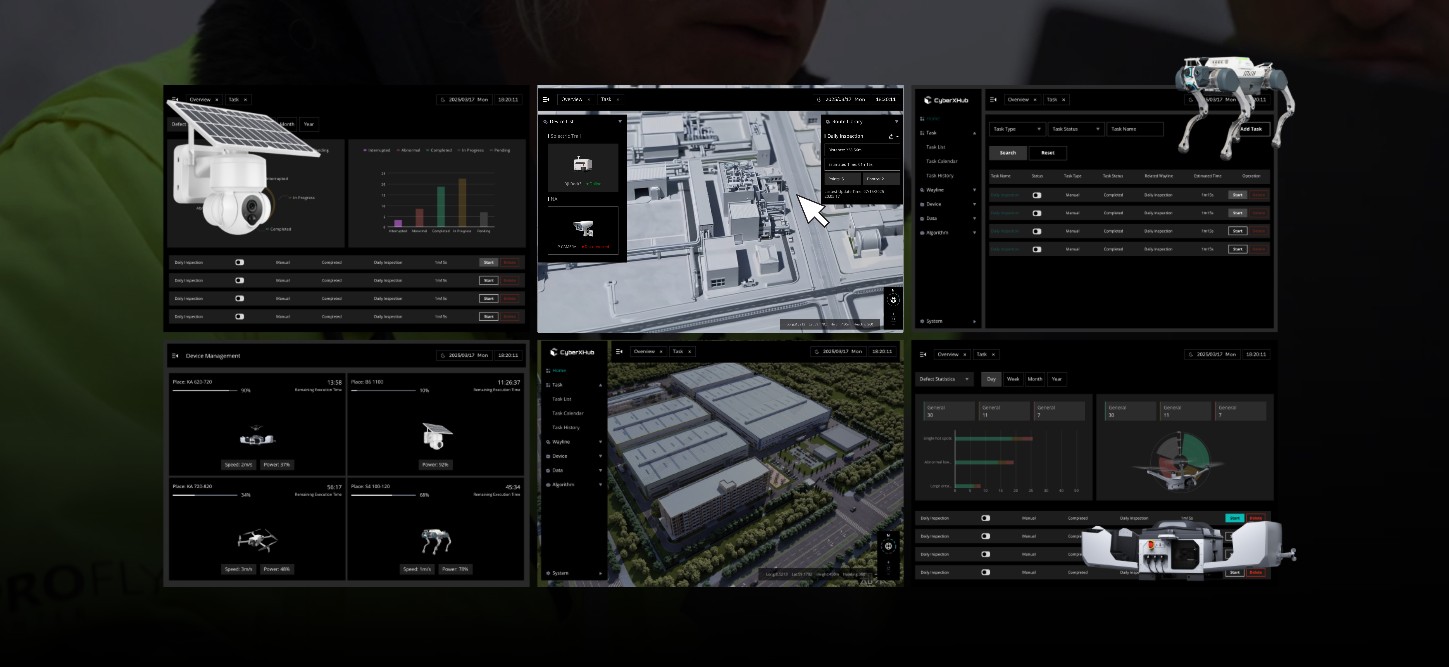
AI models are increasingly embedded in cyber operations, defense analytics, intelligence workflows, and strategic planning environments. Extracting capabilities from such systems is not simply corporate espionage. It can shorten development cycles for rival actors by years.
More troubling, distilled models often do not inherit original safeguards. The outputs can be harvested while safety layers are bypassed or stripped during retraining. That creates powerful systems without equivalent guardrails.
But the 24,000-account problem goes beyond distillation.
Mass identity fabrication demonstrates that model access control is now a geopolitical vulnerability. If adversaries can generate thousands of synthetic access points, they can not only extract capabilities but also systematically probe weaknesses, test boundaries, and explore behavioral edges.
Extraction is about copying power.
Influence is about shaping it.
Modern AI systems are shaped by interaction. Structured probing at scale can map model tendencies, discover exploitable patterns, and potentially guide downstream training in targeted ways. When access control collapses, strategic control weakens.
This is why the focus should not only be on distillation as a concept, but on the industrialization of access abuse.
Twenty-four thousand fraudulent accounts is not noise. It signals intent, coordination, and resources.
It suggests that frontier AI systems are already treated as high-value strategic assets worth systematic exploitation.
AI sovereignty is often framed as prestige or innovation leadership. But sovereignty is not about who publishes the best benchmark results. It is about who controls access, identity, infrastructure, and defensive architecture.
Dependency creates vulnerability. Weak identity systems create leverage.
The real question is not whether distillation will happen. It will.
The question is whether model providers and governments can prevent industrial-scale identity manipulation from becoming the standard operating procedure in the AI race.
Because once 24,000 fake doors exist, the battlefield is no longer theoretical.
It is operational.